
Alok Menghrajani
Currently: security consulting and lecturer.
Previously: security engineering at Square Block. Co-author of Hack (the programming language) and put the 's' in https at Facebook Meta. Maker of various CTF puzzles.
This blog does not use any tracking cookies and does not serve any ads. Enjoy your anonymity; I have no idea who you are, where you came from, and where you are headed to. Keep the dream of an Internet from times past alive.
Home | Contact me | Github | RSS feed | Consulting services | Tools & games
This post is split in multiple parts. Make sure you first read part 1.
Before I dive into how the Kaleidoscope code works, I wanted to answer the following question: how do I know the code I'm looking at is the original code?
The answer to this question is related to supply chain security. The short answer is that we can't be 100% sure unless the original code was digitally signed and there's a way to reliably check the key's integrity & ownership. The code predates publication of asymmetric key cryptosystems by a year and widespread adoption of tools such as GPG by two decades! Assuming arguendo, the code was published with a public key signature and the key size/algorithm choice didn't turn out to be weak. We would have to trust that the key has been stored physically and logically securely for 40+ years. We would have to trust the key's owner identity. Finally, we would have to trust our own modern computer which performs the signature verification operation. It turns out that supply chain security is turtles all the way down!
We can however have some level of confidence that the code is the original code. First, there's Youtube video which looks similar. Then, there's the punch card picture. The punch card is partially visible and we can extract 22 bytes to check they match the source code. Finally, Harry Garland, who co-founded Cromemco Inc., reached out to me. In all three cases, we wouldn't spot a minor code difference but we do end up with some confidence that the code we have today is the original code.
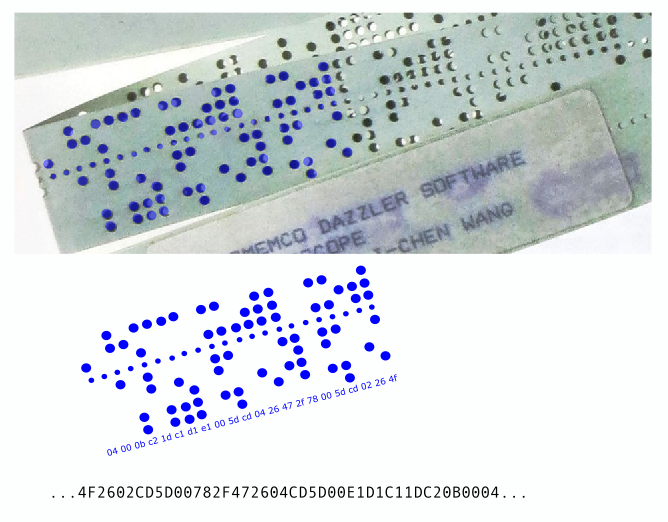
The punchcard bytes match instructions 003A to 004F! Part 3 looks at the code's control flow. In a subsequent post, I will explain how the code actually works.